DRAG USE ONLY
CODE WORD: DRAG
NSP 670C
Perception Management, Propaganda and Deception
Instructor: Fred Cohen
By:
Michael Adams
Charlie Riley
David York
Brian Younger
Outline
Introduction
Methodology
Techniques/Mechanisms
Creation of Personae
Target
OPSEC Plan
Each Weeks Goals
Expected and Unexpected Outcomes
DRAG Weekly Timeline
Graphs
Posting Activity Chart 1
Posting Activity Chart 2
Appendices
Appendix I: Target Folders
Appendix II: Activity Charts
Appendix III: Email Log
Introduction
During the Fall semester 2004, the students of NSP 670C (Perception Management, Propaganda and Deception) were tasked to complete a project involving a high-level group deception. The scope of the project involved infiltration and manipulation of an information warfare forum hosted by Fred Cohen, the instructor of NSP 670C.
Principally, members of the IWAR forum consist of experienced technical experts throughout a variety of fields focused on information security and warfare. Ultimately, the goal of the project was to use proximate and distant level group deception techniques to alter the focus of the forum to Chinese information warfare, convincing the members of the forum that China has actively engaged in information warfare against the U.S. and is in a position to win the information war.
The code name for the project was Drag, short for Red Dragon, and all communication concerning the project took place through the drag@unhca.com email address.
The basis of the project was developed from the article Did China Win the War? by Dr. Fred Cohen; it can be viewed at Dr. Cohen’s website http://all.net. Using the factors weighed by Dr. Cohen in the article consistent with a Chinese information warfare victory, the class redirected the forum to the topic of Chinese information warfare utilizing the following handles:
Current Chinese information warfare capabilities.
Incidences where China has engaged in information warfare.
The practicality that China is actively and aggressively conducting information warfare against the U.S.
Known and possible U.S. responses to China information warfare incidences and capabilities.
The possibility that China has won the information war against the U.S.
The initial objectives of the class were to:
Conduct intelligence on the forum involving the topics of previous discussions. As well, each student in the class identified one to two target individuals and conducted intelligence and background investigations on the targets. This would allow each student to identify with the background of members in the forum.
Infiltrate the forum using falsified identities with a relational background to the focus of the forum for the purpose of acceptance as equals within the forum, hiding the class deception project, and creating a legitimacy concerning the subject of our posts.
Submit posts consistent with each target to illicit an initial response. This was to test the effectiveness of the intelligence and background investigation on the targets and to develop a sense of understanding for the reaction of each target.
Slowly change the focus of the forum to the topic of Chinese information warfare, while increasing the sense of urgency in successive posts to elicit, or induce emotional concern over Chinese information warfare.
Additionally, direct communications were conducted with several targets to elicit a response of concern to the focus of information warfare.
Methodology
Considering the network organizational structure of the IWAR forum, a group level deception was necessary based on the influential requirements for such a technically proficient group of individuals. The group level deception was based on the notion of social engineering, defined by the management of human beings in accordance with their place and function in society. This is a social science that is widely used in various contexts though is especially pertinent to achieve a group level deception. To effectively implement our social engineering skills within this project, we considered the following aspects of a Group level deception, including:
Understanding the group’s dynamics and situation.
Understand who to move where in the group
Create social pressures for the desired movement within the group and the necessary support for this movement.
An effective implementation of the previous aspects will then produce group think. Group think is distinguished by a pattern of thought characterized by self-deception, forced manufacture of consent, and conformity to group values and ethics.
In order to understand the forums dynamics it was necessary to monitor and gather intelligence on the members in the forum and the history of the forum in general. Detail of the intelligence process will be described later, though it is important to understand the initial approach at this time.
We first had to define the organizational structure of the forum. The classical organizational structures defining a group are: hierarchy (i.e. military); star (i.e. everyone reports to one person); matrix (i.e. product managers vs. line managers); and a network (i.e. a loose knit organization). The IWAR forum can be considered a network organizational structure. It’s devised of a loose knit structure where a “monitor” participates and most importantly has overview of the operation of the forum, though the monitor does not necessarily hold any more power than the rest of the members in the forum. All the members are free to express their opinions at will. With the history of the forum understood, we were than able to gather intelligence and monitor individual forum member’s activities. This allowed us to understand the characteristics of these individuals and most importantly understand who is influential in the group.
Upon identifying influential assets in the forum, we were able to decide when and who we were going to interact with. By potentially moving or convincing the influential players within the forum, we could further the opportunity to achieve our goal. Membership power along with influential roles in a group creates relationships that would otherwise not be apparent. If we could convince these particular individuals within the group that China has won the information war, than others quite possibly would conform to this notion. In other words this would be creating groupthink.
To be able to move these selected individuals and as a result the entire forum to our desired goal, we had to create various social pressures. Social pressures are techniques that contribute to a group level deception. Though, these are not the only deceptive techniques relevant at this level of deception. We detail all the techniques used later in the report, though it is important to understand the fundamentals of social pressures at this time. The pressures can be obtained through the following: reinforcement for conformance and punishment for nonconformance; imitating the characteristics of the group or group members; and using authority and stature to induce a desired change.
Once we identified particular members, engaged in conversation with these members, and finally influenced them through social pressures and other deceptive techniques, we then supported their movements. When our desired change had occurred and member(s) had conformed to our notion, we then supported their change. By reinforcing a member’s post that is congruent with our goal we were able to support our desired movements.
Techniques/Mechanisms:
We were able to achieve our goal by inducing and suppressing the cognitive limitations of forum members through various deception techniques. First we will reiterate the techniques or social pressures that are unique to achieve a group level deception. Second we will describe the range of techniques identified by but not limited to experts in deception such as Chuck Whitlock, Fay Faron, Bob Fellows, Thomas Gilovich, Charles West, Chester Karrass, Cialdini, and Greene. Using the techniques defined and categorized by these professionals helped us obtain our goal..
Social Pressures:
Reinforcement: punishment and rewards for behavior;
Imitation: similar characteristics to the group;
Authority and stature: expertise and organizational affiliation induces conformance.
Other Techniques:
Contextual association: induce a plausible theory that people tend to believe;
Law of small numbers: use of several examples which are over applied;
Over application of representative ness: the few examples given are taken as more significant than they actually are;
Clustering illusion: events appear to be correlated when they are not;
Use of ambiguous data: interpret ambiguous data in the context you are looking for;
Distortions in the name of in-formativeness: stories are told with exaggerations to make a point;
The creation of casual theories: create theories to explain regardless of evidence;
Misrepresentation of incomplete or unrepresentative data: data used in context that was not originated in to validate a claim;
Reciprocation: creates influence and compliance;
Making other people come to you: control of the target making them act as a consequence of your actions;
Automaticity: default decision process that creates pattern matching to known social behavioral patterns;
Elicitation: to draw out information of a response;
Cognitive dissonance: psychological conflict resulting from inconsistent beliefs and attitudes;
*See cause and effect chart in appendix for application of these techniques/mechanisms.
Creation of Personae
To achieve concealment of our true identities we created personas using various techniques. These techniques are advantageous when conducting a group deception. We needed to include the appropriate mixture of characteristics in our personas to achieve credibility. By including organizational affiliations, accredited positions within these organizations, professional qualifications, and backgrounds and experience we were able to establish this credibility. Once created we did not want to affiliate our identities with the group all at once but instead over time. The latter would not only look suspicious but it would most importantly divulge our alliance. The purpose was to be perceived as independent from one another. With this established we combined our view or in some cases disagreed to influence group think. The following describes the personas we created and the characteristics we formulated:
Eemannucla (Riley)
Studied at UCLA
Former work:
Lockheed-Martin
Various government contracts
Age: 78
Charles Taylor (Younger)
AKA: charlest415;
Consultant for firm (name unspecified to propose confidentiality) that is interested in China and their IWAR capabilities;
Conducted numerous intelligence gathering tasks for various firms;
An unspecified security clearance;
Extensive interest in IWAR.
Mikea_xl (Adams)
IWAR hobbyist;
Concerned about overuse of natural resources and construction materials internationally, mostly China;
Commercial Construction Professional;
Project engineer for the Navicite datacenter in 2000;
Project engineer for the telecom switch in Rancho Cordova for MCI/Quest in 1997;
Project engineer for the Satellite facility at Lockheed Martin in 1996;
Completed projects for Applied Materials and KLA/Tencor.
Darrel Van Horn (Adams)
Former military experience;
Current Department of Defense employee or contractor;
Current information systems security “red team” member;
Signature line: “The
statements above do not necessarily reflect the
opinion
of my employer, my clients or the US
Department
of Defense.”;
Interested in China’s capabilities;
An unspecified security clearance.
Benicio Mondragon (York)
Immigrant from Latin America;
PhD in Molecular Genetics;
Little knowledge of IWAR though a new interest
Target
To establish a successful group level deception we had to effectively define our targets. We did so by categorizing them as direct targets and indirect targets.
Our direct target was the IWAR forum and its members. In order to conclude a “victory” at the end of the deception the direct targets must meet certain criteria. The criteria is as follows: there must be a consensus amongst the targets that China has a plan; China has had measurable successes in formulating and even implementing information warfare; and there are potential desired consequences for the U.S. and entire Western world.
Our indirect target was the media and the public around the world. Measurement for success was never formulated for the indirect targets. The indirect targets were a mere bi-product of the group level deception. If they had been successful, our deception only worked that much better than anticipated.
Furthermore, it was important to know as much as possible about our targets. Therefore we gathered intelligence not only on the entire forum but also the members of the forum. To do this we created a portfolio of the forum. This included who talked to whom and who was influential in the group. We also included intelligence about the member’s characteristics, cultures, occupations, expertise, hobbies, and interests. With this information we were able to strategize our posts to effectively manipulate the members to our desired goals. We could accurately apply various deceptive techniques by knowing the characteristics that the members portrayed. See profiles in appendix for application of complete intelligence gathering.
OPSEC Plan
To fulfill our objectives and goals we needed to be sure off all possible outcomes at each stage of the process. The difficulties associated with a group level deception are numerous. Most importantly it is essential that the deception is not divulged to the target. It was vital to control what the targets saw of us. In order to achieve this we had to create an Operation Security Plan. Some of these concerns were obvious and well planned for and others were never assumed potentially exposing the operation. Those that were unanticipated will be discussed within the unexpected outcomes portion of this report. Otherwise the following were the concerns originally addressed:
The posts on the IWAR forum at the initial stage of the project were seldom. Therefore we needed to infiltrate the group without being detected. This was demonstrated through the creation of our personas;
Constantly supporting each other could result in suspicious activity. Therefore counter claims were needed during specific stages;
Questioning targets credibility could create probe into our own credibility. Therefore we avoided this and only questioned the validity of information in regards to the issue at hand;
Likewise we could not question each others credibility during any counter claims only the validity of information in regards to the issue at hand;
It was pertinent to question if we knew enough at each stage. Was the next post going to trigger a response counter to our goals and more importantly potentially divulge the deception;
Do the targets have tracking mechanisms? What are their intelligence capabilities, culture, thought processes, intent, and attack capabilities?
The individual targets and entire forum threshold for detection;
It is important to include high risk of detection actions sooner and commit highest consequences resources later. For example individually infiltrating the group while avoiding detection versus over application of ambiguous or non-credible data. See weekly goals for application.
Weekly Goals
See time line in appendix for complete description.
Week 1:
Gather intelligence on forum members;
Get acquainted with the forum;
Begin introduction through personas;
Arguments:
China won the Information War;
China utilizes resources at a higher rate than US;
Viruses and worms attack US;
Possible ties to Muslim Extremism as a military distraction.
Week 2:
Forum traffic is slow therefore we need to escalate the controversy;
We need to have a credible person deny the article “China has won the war”. Employ a counter claim to the article;
Pick an individual target and get them involved in conversation.
Week 3:
Develop elicitation tactics;
We have developed type II errors of commission, too little information. Find or develop more references to produce evidence.
Increase the risk.
Directly target members through the use of fictitious emails.
Week 4:
Arguments:
China is using Muslim extremists to distract the US and India from the information war China is engaged in with the US and India.
China is with the Middle Eastern Muslim extremists because they need the oil.
China instigated the war so US would expend resources (oil) fighting the war.
The US is aligned with Pakistan against India?
Create sense of urgency that war is imminent.
Expected / Unexpected Outcomes and Conclusions
The findings and conclusions of this project suggest that deception consistent with group level participation executed in a fashion limited to distant and proximate techniques can be quite successful. For the purpose of this study, we concluded that the initial response to Chinese information warfare was one of skepticism within the context of the forum. However, within the group we provided critically verifiable and non-verifiable information resulting in the reconsideration of Chinese information warfare by several of the group members. To achieve this, members of the group swayed popular opinion through fake identities and acting as turns initially opposed to a Chinese information warfare victory and then becoming acceptant to the factor after additional posts concerning the subject.
It is impossible to predict all outcomes of a deception especially one involving many targets. We were quite successful in avoiding any unexpected outcomes. If our goals and objectives were vague or the deception was particularly enveloped, our anticipation of events might have been inaccurate. In particular, we became subject to one of our own techniques that we did not control for. This was the use of email during the later stages of the deception. We decided to target particular members through our fictitious email addresses for the purposes of actively engaging them in the discussion. Furthermore by probing these individuals we thought we might be able to divulge more information than originally gathered. The problem we encountered was the unanticipated response. Some of these targets started to question our intentions and even more our credibility. Luckily we were able to control these outcomes effectively. Other emails elicited no response at all. See email logs in appendix for further application of these unexpected outcomes.
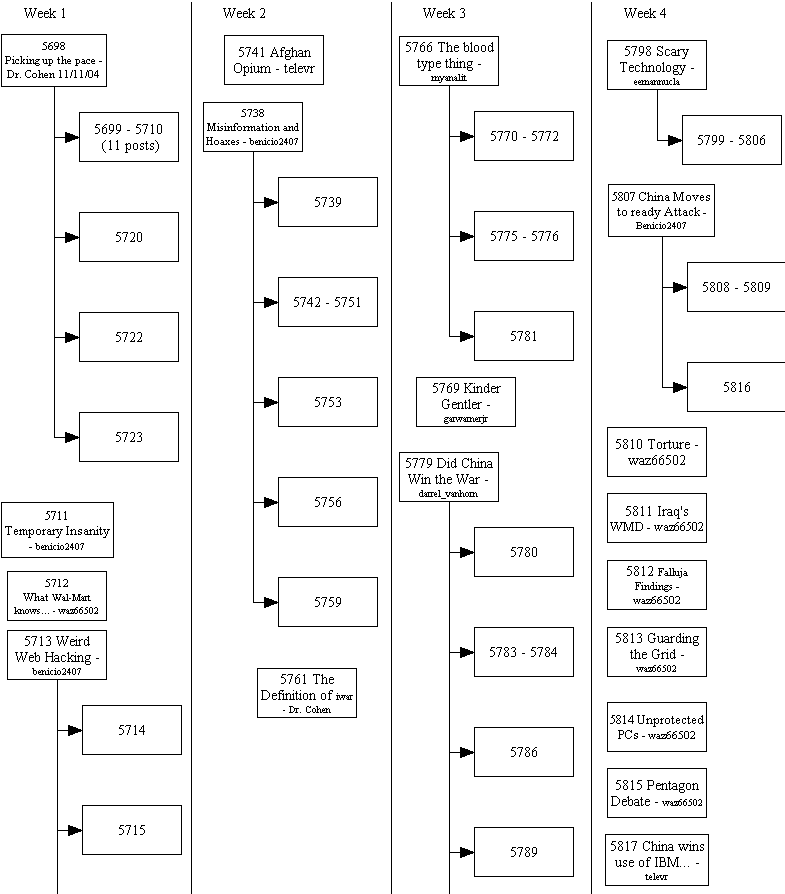
Drag Weekly Timeline
Week 1 (11/10/04 – 11/16/04):
Objectives:
Present the following ideas to the forumites:
China won the Information War.
China utilizes resources at a higher rate than US
Viruses and worms developed in and delivered by China attack US computers and critical infrastructure
Possible ties to Muslim Extremism as a military distraction
China instigates Pakistan and India
Establish a presence on the Iwar forum.
Methods:
Create personalities to use in the forum that have elements of credibility.
Read forum posts and decide on target individuals.
Create target folders for selected individuals.
Posts:
Quantity
30 posts during this period
Posts # 5698 – 5728
Topics
Professor Cohen posted a suggestion on picking up the pace of posting on the forum.
“What it is to be an American.”
“Banana Republic”
Week 2 (11/17/04 – 11/23/04):
Observations on previous activity:
Forum traffic is slow.
Some of the deceivers don’t know much about China or IWAR.
It may be worthwhile to deceive Dr. Cohen within the boundaries of this experiment.
Objectives:
We should have a credible person deny some of the statements made in deception postings.
Decide on a target individual:
Entice that person to become involved in the conversation.
Induce that person to act on the information presented.
Methods:
We need to have an easily outed person to deny the article.
Remember that we can only induce signals, it’s not possible to suppress signals within the scope of this deception.
Make posts personal to drive targets to respond.
Send private emails to targets to develop interest in the subject or to establish/destroy credibility.
Posts:
Quantity
32 posts during this period
Posts # 5729 - 5761
Topics
(12) Chinese Information Warfare posts
(2) Responses to “Banana Republic” post
(15) Responses to “Misinformation and Hoaxes”
Week 3 (11/24/04 – 11/30/04):
Observations on previous activity:
Activity is picking up.
Some of “Benecio’s” posts are initiating conversation.
“The blood-type thing” is a hot topic.
Objectives:
Continue to build credibility
Start pushing the China stories
Methods:
Use elicitation techniques: “Does anybody have any contacts in China?” “Does anyone know about Chinese petroleum usage?”
Subplot: China using Linux, not Microsoft. Obscure reference and associate with 3 disassociated articles. (Commission Type 2, not enough information.)
Make spurious web links.
“The dog tag thing (re: “The blood-type thing” postings) won’t work but there are some other things that will. We’ve seen patterns…”
“We had China infowar wargames until 9/11. Now because 3000 people have been killed it’s sitting on a shelf. These wargames had 100,000’s of casualties…”
Need cognitive resonance, baby steps.
Schedule: Running out of time… Pick up pace. Increase risk.
Personal emails to targets: “Have we met? Your name sounds familiar… Can you explain this to me?”
Posts:
Quantity
34 posts during this period
Posts # 5762 – 5796
(5) Individual emails were sent to targeted individuals
Topics
(8) Chinese Information Warfare posts
(7) Blood Type IW posts
(3) Information Warfare turned Terrorism posts
(8) Did China Win the War, Dr. Cohen? Posts
(3) Chinese-American iwar realpolitik posts (initiated by myanalit)
Week 4 (12/1/04 – 12/8/04):
Observations on previous activity:
Toni Bartoletti has accepted the thesis “China has won the infowar” and says “…so what?”
Large amounts of posts about China
Objectives:
Create a sense of urgency. “Need to act now!” “This is happening right under our noses.”
Engage Ravi VS Prasad (newspaper columnist) and convince him that he should write an article about Chinese information warfare.
Methods:
Subplot: China is using muslim extremists to distract the US and India from the infowar china is engaged in with the US and India. China is with the middle eastern muslim extremists because they need the oil. China instigated the war so US would expend resources (oil) fighting the war.
Subplot: significant date:for December 11, 1929 China Baise and Longzhou Uprisings. Quelled on December 15 with a dramatic defeat over western trained forces.
Subplot: China is building troops on the Kashmir border and allied with Pakistan.
Why?
China wants India’s engineering, software and helpdesk capabilities.
How?
China link to middle eastern groups.
Financial transactions before 9/11 is happening again in selected stocks. China is going to drop its investment.
Create sense of urgency… correlation with a date.
Posts:
Quantity
26 posts during this period
Posts # 5797 - 5822
(5) Follow-up emails were sent to targeted individuals
Topics
(9) “Scary Technology” posts
(4) “China Moves to Attack” posts
(4) “More on China” posts
(1) “China wins use of IBM brand” post (Initiated b
Activity Graphs
|
|
Posts per month 2004 |
Posts per month 2003 |
Posts/Month Without Deceiver's Posts |
|
September |
4 |
3 |
0 |
|
October |
3 |
7 |
0 |
|
November |
115 |
29 |
88 |
|
December |
26 |
73 |
21 |
|
|
Average posts per day 2004 |
Average posts per day 2003 |
Average Without Deceiver's Posts |
|
September |
0.1 |
0.1 |
0 |
|
October |
0.1 |
0.2 |
0 |
|
November |
3.8 |
1.0 |
2.9 |
|
December |
1.9 |
2.4 |
1.9 |
Drag Deception Experiment Branch Diagram of All Posts
| Poster | Topic | Purpose | Target | Mechanisms |
| darrel_vanhorn (Adams) | Missing the poington (sic) Chinese Information Warfare | Establish credibility, Engage and disagree with "Benecio", Establish that China is a threat. Introduce the conclusion that Chinese cyber-attacks are well documented and accepted as fact by "professionals" in the industry. | General: iwar forum Specific: Tony Bartolitti (called out by name and employer in post) | Build credibilityand establish authority by lying about experience and implying that statements made in posts must be disassociated with the US DoD. Create dissonance with "Benicio" to enlist forumites to take sides (either side agrees with a deceiver). Introduce factual chinese espionage investigations and link them to our topic (overapplication of representativeness). |
| darrel_vanhorn (Adams) | Re: [iwar] Re: Chinese Information "Warfare" | Continue to disagree with Benecio, introduce the theory that China is overusing resources intentionally and that threatens the US, link the apparent cessation of computer virus/worm attacks originating in China after 9/11 to China involvement in planning or funding the 9/11 attacks. | General: iwar forum | Create dissonance and the illusion of choice by presenting the issue as black or white, the targets are likely to support one of the deceivers because they don't like the message of the other deceiver (disassociate). Present ambiguous information to generate pattern assymetries (targets may recall not hearing about Chinese computer attacks soon after 9/11 but that does not necessarily link them) |
| darrel_vanhorn (Adams) | Re: [iwar] The blood type thing and IW | Establish credibility as a military man and expert in the iwar field, engage Tony Bartoletti to expand access, to exploit. | Specific: Tony Bartoletti General: iwar forum | Create resonance by agreeing with target about an inconsequential point and appearing fair and reasonable. |
| darrel_vanhorn (Adams) | Re: [iwar] The blood type thing and IW | Respond to "mikea_xl's" post (below, asking for clarification), suggest US awareness of adversaries iwar activities | General: iwar forum | Respond to question posed by another deceiver personality (mike_axl) using the rule of threes (Pakistan, China, Turkey) to lend credibility to "mikea_xl's" assertion that China is overusing resources to the detriment of the US. The Chinese example was not placed first or last to minimize its effect (too early to tip our hand). |
| darrel_vanhorn (Adams) | Re: [iwar] Information Warfare turned Terrorism | Respond to "benicio's" post, supporting points made and confirming his selection of reference material, introduce Dr. Cohen's "Did China Win the War" paper | General: iwar forum | Create resonance by agreeing with deceiver. Confirm "benecio's" expertise by acknowledging his reference material as valid and relevant. The iwar forum appears to be influenced by reinforcement, suggesting an article by expert Dr. Cohen enhances credibility and likeing of message. |
| darrel_vanhorn (Adams) | Did China Win the War, Dr. Cohen? | Post Dr. Cohen's paper "Did China Win the War?" | General: iwar forum | The iwar forum appears to be influenced by reinforcement, posting an article by expert Dr. Cohen enhances credibility and likeing of message. |
| darrel_vanhorn (Adams) | Re: [iwar] Lycos UK couinter-attacks spammers | Post sarcastic remarks in response to televr | General: iwar forum Specific: televr | Create dissonance and engage televr in a conversation to promote increased access and influence. Ultimate goal to allow televr to "convince" and "win the point", feel like a respected peer, optomistic self assessment. "darrel_vanhorn" will appear fair and reasonable. |
| mikea_xl (Adams) | Re: [iwar] Re: Misinformation and Hoaxes according to Vmyths.com | Affirmatively respond to "eemannucla's" post about China by suggesting that reporting of Chinese iwar attacks was vigorous prior to 9/11 and has stopped since. | General: iwar forum | Create resonance by agreeing with deceiver. Lie about research completed on the topic and distort information given due to plausibility based on the relative dates of the events. |
| mikea_xl (Adams) | Re: [iwar] The blood type thing and IW | Establish personality as a "simple" man. | General: iwar forum Specific: myanalit | Use Little Brother tactics to establish "mikea_xl" as a neophyte or noob in need of guidance on this topic from established members of the forum. |
| mikea_xl (Adams) | Re: [iwar] Re: Did China Win the War? | "Have we met? I'm sure we have…" | Ross Stapleton Gray | Create resonance by having common backgrounds and experience. Use access to increase influence. |
| mikea_xl (Adams) | Re: [iwar] RE: [cisspforum] Re: Homeland security chief Ridge to resign | "Have we met? I'm sure we have…" | televr | Create resonance by having common backgrounds and experience. Use access to increase influence. |
| mikea_xl (Adams) | Re: [iwar] Re: Did China Win the War? | "Have we met? I'm sure we have…" | Ross A. Leo | Create resonance by having common backgrounds and experience. Use access to increase influence. |
| mikea_xl (Adams) | Re: [iwar] Did China Win the War, Dr. Cohen? | "Have we met? I'm sure we have…" | Rob Rosenberger | Create resonance by having common backgrounds and experience. Use access to increase influence. |
| mikea_xl (Adams) | Re: [iwar] Re: Did China Win the War? | "Have we met? I'm sure we have…" | Tony Bartoletti | Create resonance by having common backgrounds and experience. Use access to increase influence. |
| mikea_xl (Adams) | RE: [cisspforum] Re: Homeland security chief Ridge to resign | Reply to Ross A. Leo's response to "mikea_xl's" personal email, vague association with past events, ask opinion of the "China infowar issue" | Ross A. Leo | Create resonance by confirming common background and experience, use acces to increase influence and ask about China. "mikea_xl" is using the Little Brother approach in the public forum and continues here by asking opinion and guidance. |
| mikea_xl (Adams) | Re: [iwar] Re: Did China Win the War? | Reply to Ross Stapleton Gray's response to "mikea_xl's" personal email, establish credibility as a non-expert in this field, ask about China infowar posting activity on forum and target's opinion, propose Tony Bartoletti's opinion "who cares?" | Ross Stapleton Gray | Create resonance by confirming common background and experience, use acces to increase influence and ask about China. "mikea_xl" is using the Little Brother approach in the public forum and continues here by asking opinion and guidance. |
| mikea_xl (Adams) | RE: [cisspforum] Re: Homeland security chief Ridge to resign | Reply to Ross A. Leo's response to "mikea_xl's" personal email, expand on Ross A. Leo's stated opinion that China wants to be free from western influences, introduce the idea that china and middle-east are similar that way, | Ross A. Leo | Create resonance by confirming common background and experience, use acces to increase influence and ask about China. "mikea_xl" is using the Little Brother approach in the public forum and continues here by asking opinion and guidance. Steer the conversation toward the weekly goal of establishing a middle-east / China link. |
| mikea_xl (Adams) | RE: [cisspforum] Re: Homeland security chief Ridge to resign | Damage control response : possible detection of deception! Ross A. Leo challenged credibility of "mikea_xl" in email reply but did not challenge the message. The challenge is accepted and refuted, "mikea_xl's experience is verifiable and detalis are provided, apologies are offered. | Ross A. Leo | Deflect the possible detection by providing true and accurate details of experience confirming identity as stated in a qualified confession. If Ross A. Leo chooses to verify he will find that all information given is true and accurate. Confirming "mikea_xl's" identity is intended to induce the tendency to seek confimatory data, (if this is legitimate, that must be legitimate as well). Ross A. Leo is likely to be receptive to subsequent messages due to recriprocation if the apology is accepted. |
| Charlest415 on 11/17 (Younger) | China Information Warfare | Intoduction to the forum; Response to "China wins the war" article; China's economic dominance; Divert the attention of China vsTaiwan to China vs. U.S.; opportunity for China to conduct IWAR; | General: iwar forum | Mid level deception: Studied the target to test their responses; Contextual association: induced a plausible theory that people tend to believe; Law of small numbers: used several examples which were hoped to be over applied; Group level deception: Induction of imitation and authority through professional, background, & organizational affiliation. |
| Charlest415 on 11/21 (Younger) | Re: Chinese Information "Warfare" | Response to Benicio (David) playing devils advocate about the China threat; Intelligence Capabilities that contribute to IWAR; Chinas capability to topple the U.S. interdependent civilian infrastructure; China's presence in the U.S. creates a concern for espionage. | General: iwar forum Specific: Rob Rossenberg: response to his definition of when it is really warfare; Toni Bartoletti: response to his definition of warfare. | Mid level and group level deception: Induction of authority through proclaimed professional background; Over application of representative ness: the few examples given are taken as more significant than they actually are; Clustering illusion: induced events being corelated and suppressed the fact that they are not. |
| Charlest415 on 11/29 (Younger) | Re: [iwar] The blood type thing and IW; IWAR attacks on infrastructures and by non-state actors | Response to Benicio (David) "information warfare turned terrorism"; Indirect response to Ross Stapleton Gray inorder to further involve him with topic; The possibility of China conducting State sponsored terrorism. | General: iwar forum Specific: Ross Stapleton Gray | Mid level and group level deception: Imitation: agreed in part with Ross commenting on his notion of non-state actors in order to get him to respond; Use of ambiguous data: induced the notion of non state actors through several scenarios; Misdirection: tried to change the forum topic to China sponsoring terrorism; Clustering illusion: induced events appearing to be correlated and suppressed that they may not be; Distortions in story: exaggerations |
| Charlest415 on 11/30 (Younger) | Information Warfare turned Terrorism; Chinas support of terrorism | Response to Benico (David) article about "Unrestricted Warfare"; Also a follow up to my last post; Provide evidence that China does support terrorism with the intentions of creating "groupthink" concerning the issue. | General: iwar forum | Mid level and Group level deception: Imitation and conformation to Benico on "Unrestricted Warfare": "I find this article interesting as well"; Use of ambiguous data to induce a corelation; Misdirection; Clustering illusion; The creation of casual theories: induced a theory and supressed the inaccuracy of the evidence. |
| Charlest415 on 12/7 (Younger) | Re: China moves to ready attack; China's alliance in the Muslim world. | IWAR by China is not strictly U.S. aimed, also India & Pakistan; To create urgency that war is immanent; Target Ravi vs. Prasad: to lure him into discussion by citing his work; Support Benico (David) claim to this issue. | General: iwar forum Specific: Ravi Vs Prasad; Mohammad Ozair Rasheed. | Mid level and Group level: Over application of representative ness: Induced a few examples as being more significant than they actually are; Clustering illusion: events appear to be correlated though suppressed that they are not; Induced incomplete data fo create misrepresentation. |
| Charles Taylor Email to Ravi Vs Prasad on 12/7 (Younger) | The current issue: China's alliance with Muslim world | To engage Ravi in the current topic | Ravi Vs Prasad | Imitation: I induced my proclaimed expertise and knowledge to identify with his interest, expertise, and knowledge in the issue; Authority: Induce the expertise I proclaim in my persona to may make him more inclined to discuss the subject; Influence and compliance through reciprocation: the members in the forum would strongly appreciate his input at this stage in the game. |
| Benicio2407 (York) | Re: Temporary Insanity | In response to Fred Cohens comment on the state of temporary insanity in the U.S. | General: iwar forum | The mechanism was to introduce myself to the forum by responding to a comment made within the forum and to present myself as a member. This was a form of camouflage within a group of technical experts. |
| Benicio2407 (York) | Weird Web hacking nonsense from China | I introduced a simple article on web hacking in the U.S. from what seem to be a Chinese source. | General: iwar forum | The mechanism was to generate a response focused on China to create a causal theory. This would allow the rest of the deception group to chime in more on Chinese information warfare. |
| Benicio2407 (York) | Re: Banana Republic | I responded to Mohammad Ozair Rasheed by taking his definition of banana republic and applying it to Chinese Information warfare. | General: iwar forum Specific: Mohammed Ozair Rasheed | The mechanism was to use a motivational determinate to further direct the conversation of the forum toward Chinese information warfare by responding to Rasheed's post. |
| Benicio2407 (York) | Chinese Information Warfare | I began this post to direct entirely the conversation of the forum to the specific topic of Chinese Information Warfare, by implicating our current understanding of the subject and insenuating that the U.S. was focusing on it as well. | General: iwar forum | The mechanism was to use misinterpretation of incomplete or unrepresentative data in the form of a broad political statement concerning the U.S. stance toward Chinese information warfare for the purpose of illiciting a wide variety of feedback on the post. |
| Benicio2407 (York) | Misinformation and Hoaxes | The purpose of this post was to focus on a subject on of my targets was interested in and get him to respond | General: iwar forum Specific: Rob Rosenberger | The mechanism was a direct introduction of the subject area my target claims to be an expert in. |
| Benicio2407 (York) | Re: Misinformation and Hoaxes according to Vmyths.com | This post was a continuation of the my previous post chiming in on the current conversation regarding misinformation and hoaxes regarding Chinese information warfare. | General: iwar forum Specific: Rob Rosenberger | The mechanism was to provide further detail about my deception personality so as to illicit further response by stroking the ego of Mr. Rosenberger. |
| Benicio2407 (York) | Re: Chinese Information "Warfare" | The misinformation and hoaxes conversation was leading away from the Chinese focus to I reintroduced Chinese information warfare in the context of misinformation and hoaxes. | General: iwar forum | The mechanism was to regenerate a focus toward Chinese information warfare by introducing a concept of misinformation coming from China about their Iwar capabilities. |
| Benicio2407 (York) | Information Warfare turned Terrorism | This post introduced the concept that China may be involved with funding Islamic terrorist aimed at attacking the U.S. | General: iwar forum | The mechanism was to use motivational determinates or belief regarding the very potent subject of linking Chinese information warfare so as to generate strong responses from the forum members. |
| Benicio2407 (York) | Re: Did China win the war? | This is were I tried to set the hook for China being involved with terrorism. It was in response to Fred Cohen's article "Did China win the war?" | General: iwar forum | The mechanism was to use motivational determinates or belief regarding the very potent subject of linking Chinese information warfare so as to generate strong responses from the forum members. |
| Benicio2407 (York) | China moves to ready attack | This post was to introduce the concept of China linking up with Pakistan for the purpose of combating U.S. military support to India. | General: iwar forum | The mechanism was to use base rate departures by generating several fake articles with bogus links to introduce supposed facts about Chinese strategic movements around the Kashmiri area. |
| eemannucla (Riley) | China information warfare article | This was my first post to the forum and was intended to somewhat introduce myself to the forum, and to put Dr. Cohen's article out in the open in order to lay some kind of foundation for our attack. Response: There were no direct responses to this post, but it gave other group members a platofrm to post more on China, and acted as more of a transitioning post so that the China topic didn't just seem to drop out of the blue. | General: iwar forum | This post was fishing for any responses, and employing Greene's 8th law: "When you force the other person to act, you are the one in control. It is always better to make your opponent come to you, abandoning his own plans in the process". |
| eemannucla (Riley) | Re: Misinformation and Hoaxes according to Vmyths.com | The purpose of this post was to propose a connection between China and the Middle East, and further build on the idea that China is the biggest threat to the U.S. | General: iwar forum Specific: Ravi Prasad | Reciprocation (Cialdini) was used to lure Prasad into posting. By quoting one of his articles I hoped to bring about some kind of reciprocation on his part. In other words, if I reference his work, maybe he will post in response to mine. |
| eemannucla (Riley) | Scary Technology | Further develop China as a real threat. Response: 4 forum members responded. At first there was a negative response, but affter receiving support from Dr. Cohen (credible authority) the general opinion seemed to changed towards a more positive one. | General: iwar forum | Creation of a casual theory (Gilovich). Using "expert" sources to gain credibility and authority. Using outrageous claims to illicit response [THERE HAS TO BE A BETTER WAY OF SAYING THIS ONE] |
| eemannucla (Riley) | More on China | Posted an article to further the idea that China is connected to the Middle East. Response: 1 repsonse, slightly negative. (raleoutmb) suggested that China might not be as big a threat as it's cracked up to be. | General: iwar forum | Authority and Automaticity (Cialdini). |
| eemannucla (Riley) | re:More on China | Posted another article on the China - Middle East connection. This article suggested China's connection to the Taliban and 9/11 | General: iwar forum | Authority and Automaticity (Cialdini). |