Deception Toolkit
The Deception Toolkit Home Page and Mailing List
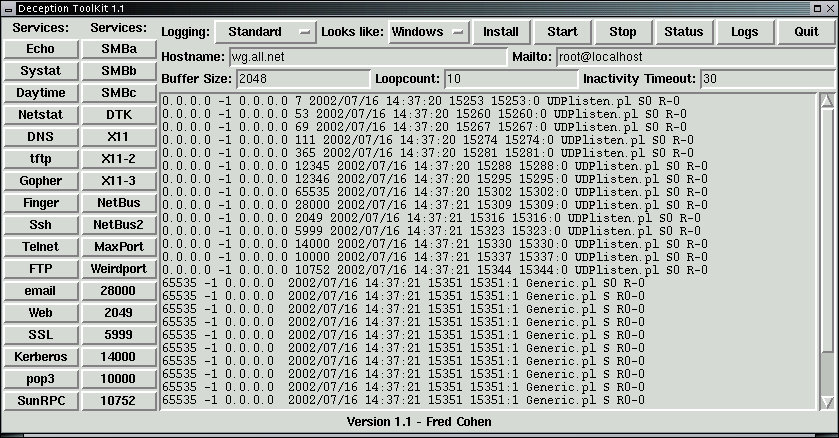
New DTK GUI Exclusively available on White Glove
Our Mission:
Our mission is to discuss issues surrounding deception and the deception
toolkit from the definition of what it is to how to do it and everywhere
between.
Rules of Engagement
Rule 1: The mailing list is fully moderated and the moderator (fc at all.net) at his sole discretion and without
recourse of any sort, reserves the right to edit entries, remove or ignore
submissions, and comment on submissions.
Rule 2: No advertising is allowed other than paid advertising
that supports the mailing list. This includes extensive signature lines,
voluminous discussions of any individual product or service, or anything
else that would tend to sell sell sell.
Rule 3: You can sign up or off the list in the same way as you
make submissions to the list. Because we are fully moderated, it all goes to
the same place anyway.
Rule 4: You will not be solicited, the list will not be sold, and
so forth. This does not mean that people will not find out about your email
address through postings to the list (unless you request that they be
anonymous), but it means we won't sell or give away the information and
there is no automatic way to get it.
Rule 5: Be polite and respectful or it won't be published - or
worse yet - I may edit it to make it civil (there's something you don't want
to have happen).
Press here to submit, sign-up, or remove
Back Issues:
19980313 -
19980315 -
19980316 -
19980318 -
19980831 -
19980904 -
19980927 -
19981014 -
19981031 -
19981107 -
19981120 -
19981210 -
19981211 -
19981212 -
19990101 -
19990102 -
19990106 -
19990123 -
19990307 -
19990326 -
19990405 -
19990409 -
19990410 -
19990412 -
19990414 -
19990420 -
19990603 -
19990615 -
19990627 -
19990720 -
19990724
Introduction and Basic Idea:
The Deception ToolKit (DTK) is a toolkit designed to give defenders a
couple of orders of magnitude advantage over attackers.
The basic idea is not new. We use deception to counter attacks. In the
case of DTK, the deception is intended to make it appear to attackers as if
the system running DTK has a large number of widely known vulnerabilities.
DTK's deception is programmable, but it is typically limited to producing
output in response to attacker input in such a way as to simulate the
behavior of a system which is vulnerable to the attackers method. This has
a few interesting side effects:
- It increases the attacker's workload because they can't easily tell
which of their attack attempts works and which fail. For example, if an
attack produces what appears to be a Unix password file, the attacker would
normally run "Crack" to try to break into the system. But if the password
file is a fake, it consumes the attackers time and effort to no result.
- It allows us to track attacker attempts at entry and respond before
they come across a vulnerability we are susceptible to. For example, when
the attacker tries to use a known Sendmail attack against our site, we record
all of their entries to track their techniques. With this deception in
place, we have no problem picking up port scans, password guessing, and all
manner of other attack attempts as they happen.
- It sours the milk - so to speak. If one person uses DTK, they can see
attacks coming well ahead of time. If a few others start using it, we will
probably exhaust the attackers and they will go somewhere else to run their
attacks. If a lot of people use DTK, the attackers will find that they need
to spend 100 times the effort to break into systems and that they have a
high risk of detection well before their attempts succeed.
- If enough people adopt DTK and work together to keep it's deceptions up
to date, we will eliminate all but the most sophistocated attackers, and
all the copy-cat attacks will be detected soon after they are released to the
wide hacking community. This will not only sour the milk, it will also up the
ante for would-be copy-cat attackers and, as a side effect, reduce the "noise"
level of attacks to allow us to more clearly see the more serious attackers and
track them down.
- If DTK becomes very widespread, one of DTK's key deceptions will become
very effective. This deception is port 365 - which we have staked a claim
for as the deception port. Port 365 indicates whether the machine you are
attempting to connect to is running a deception defense. Naturally, attackers
who wish to avoid deceptive defenses will check there first, and eventually,
simply running the deceptive defense notifier will be adequate to eliminate
many of the attackers. Of course some of us defenders will not turn on the
deception anouncement message so we can track new attack attempts by those who
avoid deceptive defenses, so... the attacker's level of uncertainty rises, and
the information world becomes a safer place to work.
See also Managing Network
Security for related articles.
Thank you